Should We Be Free To Be Anonymous Online
Should We Be Free To Be Anonymous Online
Online privacy is a thorny issue at the best of times. World-leading names such as Facebook and Google have both faced criticism within the past 12 months for appearing to ride roughshod over people’s right to privacy.
Both companies and their subsidiaries have been accused of interpreting privacy laws to suit themselves, as well imposing their own guidelines irrespective of whether they actually comply with the law in certain jurisdictions.
That said, there are many options that are available for someone who wants to remain anonymous online and take the prospect of Google, Facebook, or another company breaching our rights out of the equation.
Hiding Yourself Online
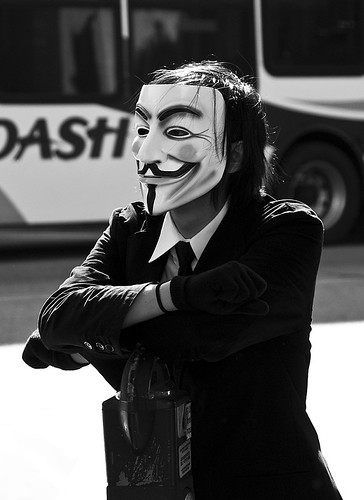
Many people decide that they are going to hide themselves online and become ‘anonymous’ so that people cannot trace who they are.
Of course, while it is understandable that people would want to use a proxy server or program if they are uncomfortable with the thought that their online habits and physical location can be identified, there is also the issue of what happens when such services and platforms are abused.
Tor: The Japanese Case
Tor – The Onion Router – is a hugely popular online service that used by many people around the world. It works by concealing a user’s IP address behind several layers of networks – the ‘onion’ effect – and so allowing a person to browse privately without leaving an electronic trace.
In Japan, Tor is currently courting controversy as a high-profile hacker, ‘Demon Killer,’ has been using the program as his shield while undertaking their ‘activities.’ This has led to the Japanese police calling for people to be banned from using such systems if they are found to be abusing it.
So far, Japanese ISPs have resisted calls for this to happen, flatly stating that it is not something they would ever entertain doing.
Should this case go higher in the Japanese court system, it will be viewed with great anticipation from around the world. There is already great debate taking place in the United Kingdom around a proposed bill that will allow police and security organizations to view the online activities of the entire population; if a leading technology nation such as Japan starts to say hidden IP addresses can be outlawed in certain situations, how long before the rest of the world follows?
The inevitable endgame, based on the way legal cases around the world tend to have gone since 2000, is that this is all going to end up in some awkward human rights wrangle.
From the police and a law enforcement perspective it sounds sensible enough, but how can they identify who is using it when the point of the program is to allow internet users to remain anonymous?
Of course, there are ways around pretty much everything, but the police involvement is potentially about to open up a whole new issue surrounding technology and the law.
Internet Use in Police Investigations
What if the police use programs such as Tor, or proxy servers, to aid their efforts during investigations? Some people will stand firmly in the ‘as long as good comes out of it’ lobby, but others will ask the question of how can they uphold the law without following it themselves?
Courts are already finding themselves unable to make convictions based on the way evidence has been collected; the outcry when a potential murderer or rapist walks free from court all because the police did not go about their business by the book can be easily imagined.
Saying the police can use a program is okay, but how long before it is abused and people are compromised? Again, there will be an underlying sense of if you have nothing to hide, you have nothing to be afraid of, but surely that should not mean a person has no right to privacy?
At some stage, someone will have to produce a white paper or an alternative document detailing why valuing privacy is a world away from having something to hide. The sooner the layperson can differentiate between the two, the quicker these issues will be able to move forward.

Cyber-Crime Issues
The fast development of technology used in cyber-crime is also going to play a part in this issue, you have to feel. Say the police are able to apprehend “Demon Killer,” surely it is only going to be a matter of time before another IP hiding tool or software is launched that is even more difficult to trace.
If people want to remain anonymous, regardless of their reasons for wanting to do so, technology will more than likely find a way.
The speed of technology development is something that the courts will have to deal with at some stage. Due to the general lack of knowledge relating to cyber-crime in regular police forces and court systems around the world, new technology can be developed and released between a person being charged and appearing in court.
This will lead to situations where the court potentially finds itself dealing with an issue that is no longer current, and therefore a huge portion of evidence in cyber-crime cases might be lost.
While the real battle here might still be between the cyber-criminals and those producing the security measures to combat it, the only real progress will be made when law enforcement agencies and the courts get a better grip of what they are dealing with.
The Right to be Anonymous
The truly unsettling aspect of this is that few of us really know how the information we are involuntarily sharing online is used, or in whose hands it ends up. If a person wants to use a program such as Tor, then that should not automatically be seen as having something to hide.
This perfectly sums up the paradox that the whole world faces when it comes to privacy. Yes, we want to enjoy our privacy and not feel like everything we do is out there ‘in the ether,’ yet at the same time privacy might be the price we pay to live in a safer world.
Perhaps the most frightening thing is that agencies and governments will potentially use that solution to their benefit, regardless of the level of threat from terrorists or cyber criminals at any one time.
Robert is an experienced IT professional, taking an interest in everything from VPS hosting and web development up to self-protection from online fraud and the value of anonymity on the internet.
featured image source